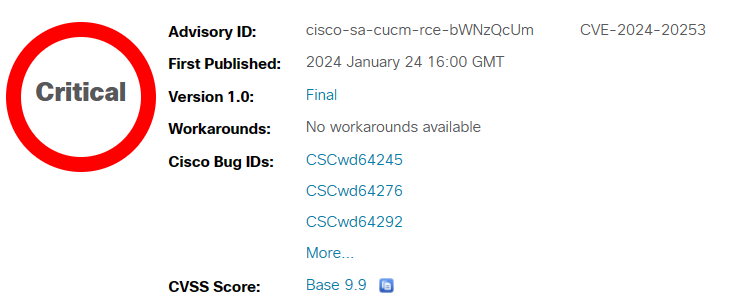
A flaw in some Cisco Unified Communications and Contact Center Solutions products could allow...
Cisco
Cisco Security Advisory was released today about the Cisco Unity Connection Unauthenticated Arbitrary File...
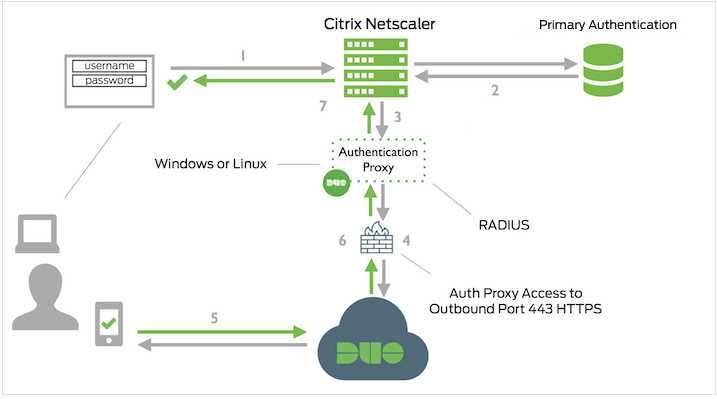
To add Duo two-factor authentication to your Citrix Gateway with nFactor you'll configure the...
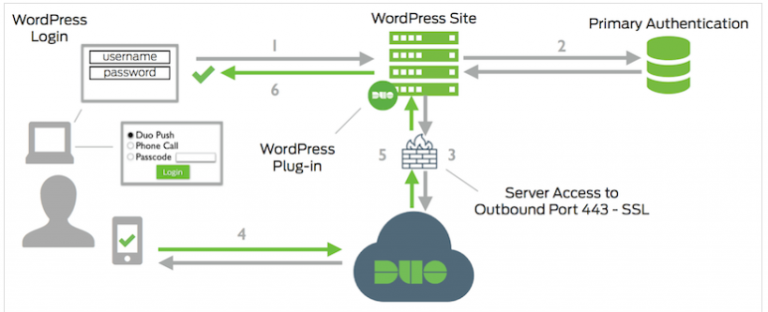
Today, I am going to show you how to configure Cisco DUO two-factor authentication...
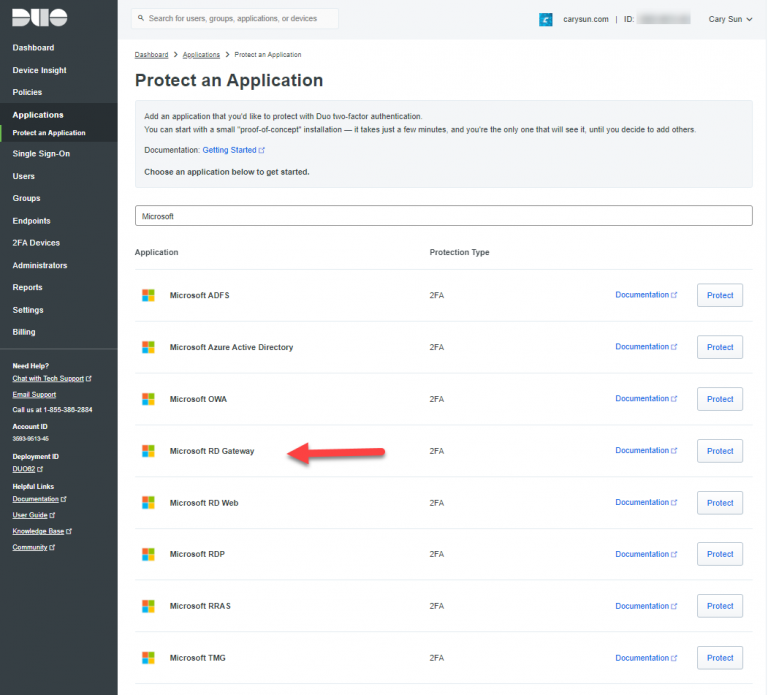
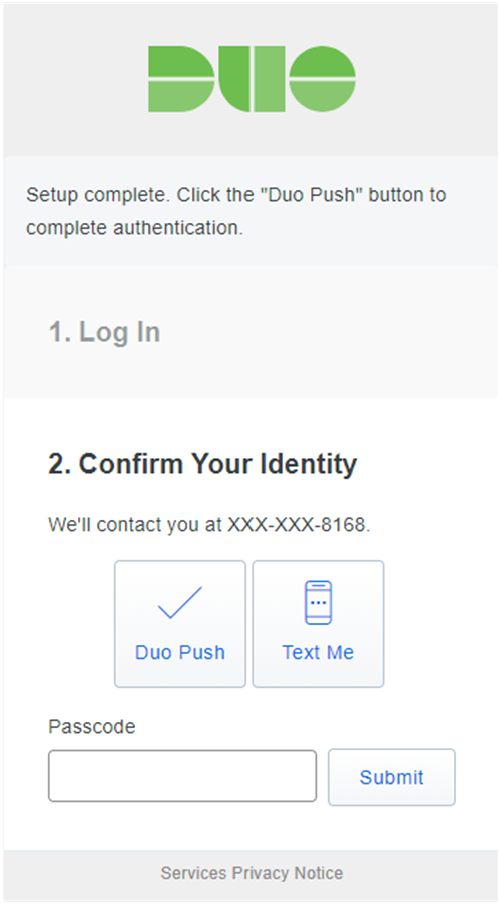
Duo Authentication for Remote Desktop Gateway adds two-factor authentication to your RemoteApp Access logons,...
Duo integrates with Microsoft Windows client and server operating systems to add two-factor authentication...
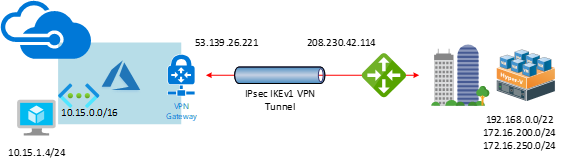
This document will show you how to step by step to configure Cisco Meraki...
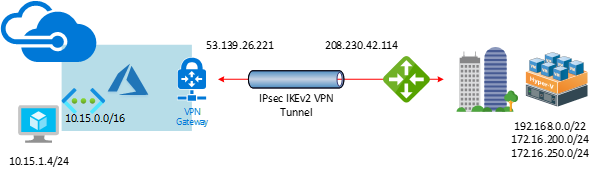
This document will show you how to step by step to configure Cisco Meraki...